Although hacking and monitoring may seem rather sinister and immoral activities, changes in our world have compelled us to assure safety and make certain that our acquaintances are protected from all the perils. Consequently, we have to guarantee protection and require something for undergoing this apparent complication.
Text messaging is a unique and worthwhile exchange of information that was introduced as the most primitive option. Text messages are undoubtedly still in use and find their use whenever we lack an internet connection. However, on a more disquieting note, text messages can be used as a vital source of harassment and scams.
Numerous hindrances arise from messaging as it is an easy and optimal method of approach towards your target. To prioritize the safety of your loved ones, you need a specific aid or a tool that can assist you in completing the security protocols, necessary for protection from the issues that are imminent in the railing society.
Spyic: The Only Tool You Require For Effortless Phone Hacking:
Features Of Spyic And Why Should You Choose It?
Spyic is the only tool that helps you to secure your children and loved ones form the digital scourges that are increasing day by day. This magnificent application tool devours all of the secrets inside the phone you want to hack and provides you with all the necessary details.
Spyic is highly reputed and a massive brand that has found its meaning and intense popularity through the brilliant and superlative services that it bestows. Several people want to hack phones and divulge the problems that are existent inside the target phones. To assure that Spyic is the most appreciated and recognized brand, you can try the text-based hacking app and check out why Spyic leaves all its competitors in the dust!
You would have guessed the captivating and miraculous characteristics of Spyic by the following passages. Additionally, it would please you to become illuminated by the fact that Spyic has been featured and appreciated in World-class digital platforms that are MacWorld, 9to5Mac, New York Magazine, Business Insider, Digital Trends and more. For dealing with all the issues regarding phone hacking, you can always rely on Spyic for efficacious and relentless hacking service 24/7.
Features That make Spyic Famous:
1) Spyic is a highly recognized and superior brand that has acclaimed far levels of fame and repute for its formidable characteristics.
2) Spyic is an all-round solution for hacking the target phone and effortlessly divulging all of the secrets that are buried deep within.
3) Spyic provides web-based ease of access for iPhone and therefore, helps in highly private besiege.
4) Spyic application can be easily installed on the target phone for free and you can easily overview the activities that are being done on the target mobile.
5) Minute 2MB size aids in maintaining the identity of the monitoring person. The application hides inside the mobile of the target and therefore, prevents identity disclosure.
6) Spyic is equipped with over 35+ brilliant application tools and benefits that make it the most trustable and sound application for hacking.
How Spyic Hacks The Target Phone?
Hacking is defamed for being an illegal activity but the technology of this era leaves us no choice than hacking someone’s phone to identify and issue the subject may illicit. Undoubtedly, Spyic has been featured and nominated for being the best and easiest solution but here are the steps that aid you further in hacking.
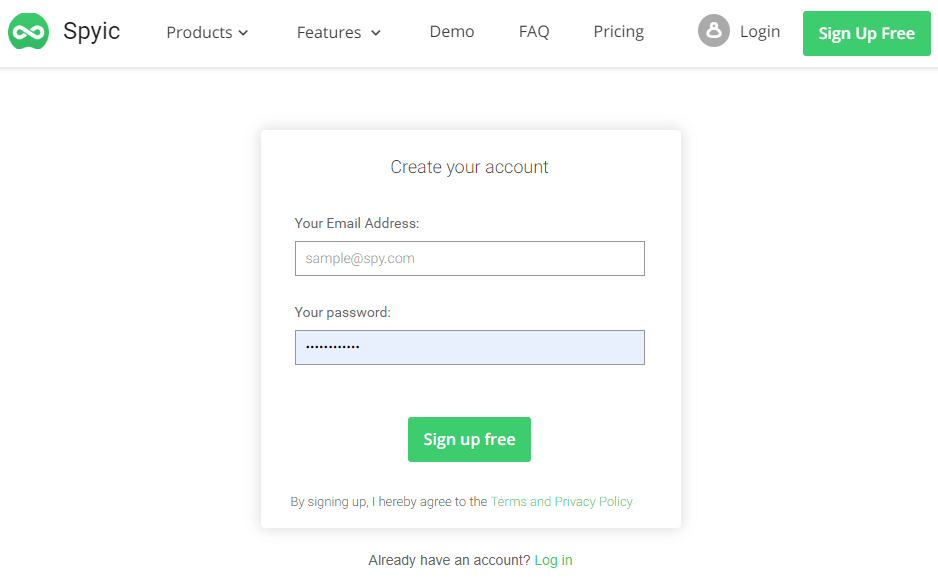
#1 Installation And Setting Up:
The first step is to allow the application to intervene in the problems that are bothering you and install it on either the target or monitoring phone. Installation is an easy procedure and is followed by signing up that requires you to confirm your account on the site to preserve your identity and ensure rights.
This will easily help in setting up and making sure that the hacking process is undertaken without any difficulty.
 #2 Providing Details:
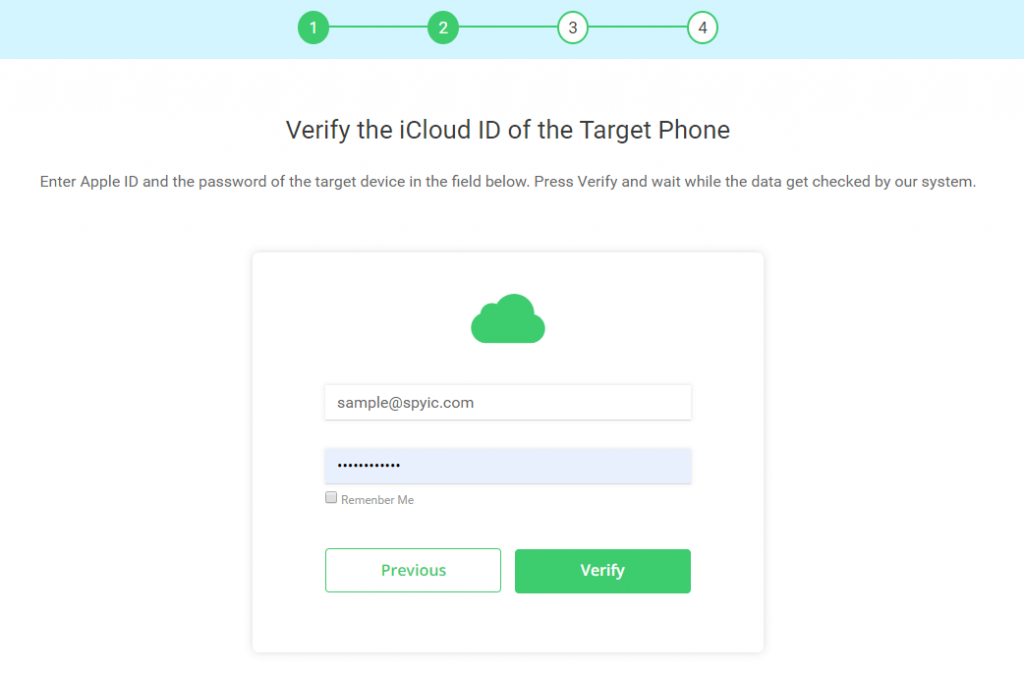
#2 Providing Details:
Since identification is a vital requirement of hacking and is a substitute for direct information, detail board opens up after installation that requires you to put in your necessary credentials.
iPhone users can provide iCloud credentials to continue the process. However, Android target phones must be accessed and have Spyic installed on them to ignite the process.
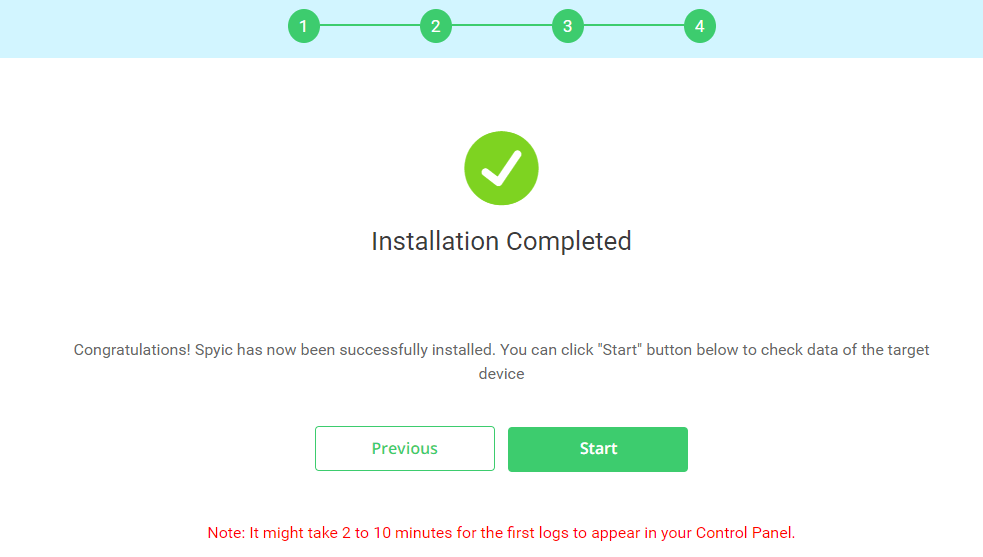
 #3 Finishing Installing And Final Setup:
#3 Finishing Installing And Final Setup:
Finish the above procedures to start your own hacking zone. This is the final setup process for the ride that you are about to enjoy. Hacking the target mobile has never been this cool!
You can enjoy all the superior benefits and privileges by installation and setting up so make sure that you provide the right details.
 #4 Divulge Text Through Dashboard Facility:
#4 Divulge Text Through Dashboard Facility:
Text messages that once made you concerned and depressed regarding your concerned ones can now be easily divulged. Several other features allow us a complete interior look of the target phone.
The dashboard facility provides you with a proper window to look inside and keep a track of your child, employee or spouse.
Reading Text Messages:
Spyic is well-aware about the adjustments or troubles that are feared to rise up deliberately due to un-watched and careless text messaging.
Spyic assures it can be relied on and hired for text message interception. Spyic is firmly hooked with all the capabilities and conventional entitlements that make it the best text interceptor. Following are the details that rectify the statement:
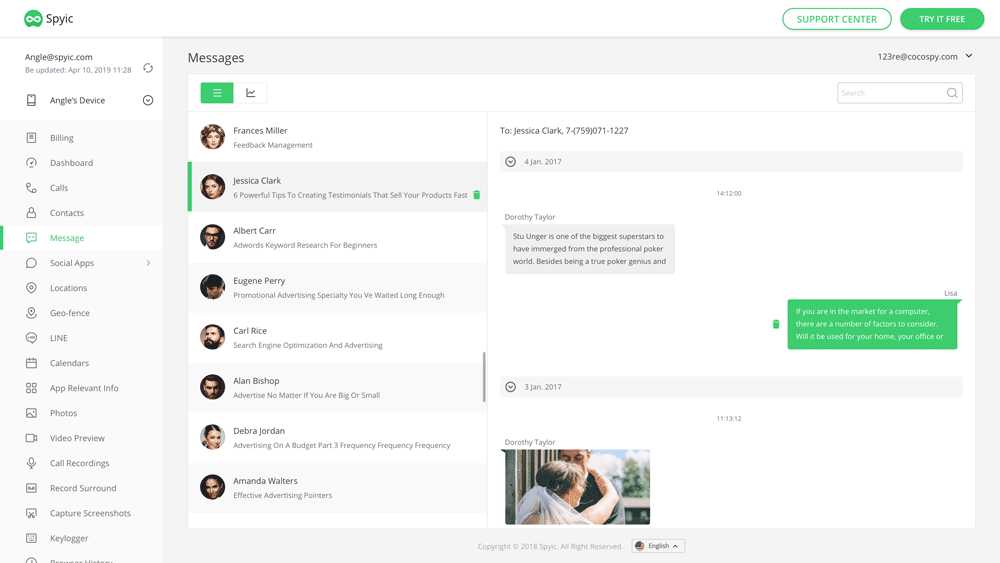 Complete analysis of the persons who are involved in texting your target phone. Details include mobile number, location, and identity.
Complete analysis of the persons who are involved in texting your target phone. Details include mobile number, location, and identity.- Compelling information about the sender and locations from where the texts were sent.
- All of the textual content and all of the protocols that were employed in forwarding or receiving.
- Secrecy and privacy in the entire process is the key of the text interceptor tool.
At The End
Spyic is a large brand that focuses on the satisfaction and fulfillment of client needs. For text message interception and general hacking, you can always choose Spyic over any other brand as the qualities it possesses are far more appreciated than any other competitor.
Spyic provides a complete insight into the activities that were once concealed form publicity. Therefore, make sure you download Spyic and revel on its aesthetic qualities!

